this post was submitted on 06 Oct 2024
736 points (91.0% liked)
Technology
59456 readers
3573 users here now
This is a most excellent place for technology news and articles.
Our Rules
- Follow the lemmy.world rules.
- Only tech related content.
- Be excellent to each another!
- Mod approved content bots can post up to 10 articles per day.
- Threads asking for personal tech support may be deleted.
- Politics threads may be removed.
- No memes allowed as posts, OK to post as comments.
- Only approved bots from the list below, to ask if your bot can be added please contact us.
- Check for duplicates before posting, duplicates may be removed
Approved Bots
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
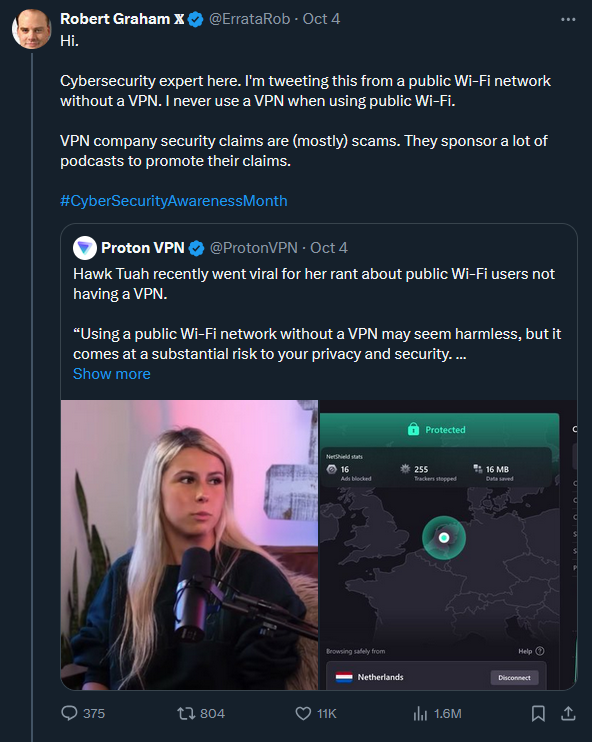
It seems like your whole threat model is avoiding DNS poisoning, which is fine, but I fail to see how you can compare using DoH/DoT to a VPN.
Except for the DNS provider (in your example, Google, so... yikes), the operator of the network you're on (since the destination IP can be rDNS'd or WHOIS'd, or simply grabbed from the Host header if your browser still tries HTTP first). Any traffic that is not encrypted will be snoopable. Traffic volume and connection times to each destination can be analyzed.
By contrast, a VPN will also use secure (if you trust the provider ofc) DNS servers for your requests, plus making all of the traffic completely opaque except for "going to this server".
You can also make your own, free VPN service with a little technical knowledge.