this post was submitted on 07 Oct 2024
187 points (99.5% liked)
Programmer Humor
1366 readers
1 users here now
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
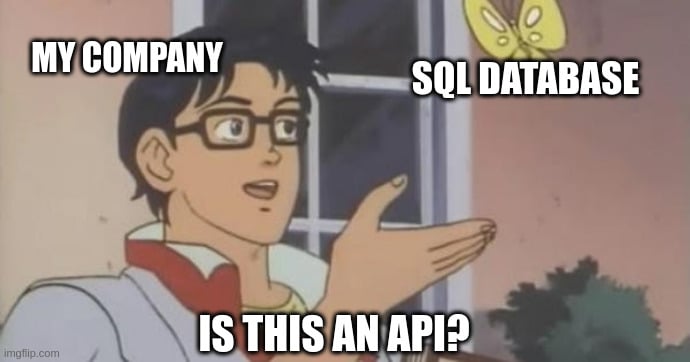
I've seen that exact type of endpoint, hitting databases in production. 🔥
If that's a pass through, that's bad.
If that's used for authentication, authorization, credential limiting, or rate limiting, then sure.
There is no context in this world validating this level of unsanitized SQL. Even for internal use this is bad, since it bypasses the auth of server and dbms.
That is a very good point.