We oughtta arrest the people who pave roads because human traffickers use them to commit crimes.
Technology
A nice place to discuss rumors, happenings, innovations, and challenges in the technology sphere. We also welcome discussions on the intersections of technology and society. If it’s technological news or discussion of technology, it probably belongs here.
Remember the overriding ethos on Beehaw: Be(e) Nice. Each user you encounter here is a person, and should be treated with kindness (even if they’re wrong, or use a Linux distro you don’t like). Personal attacks will not be tolerated.
Subcommunities on Beehaw:
This community's icon was made by Aaron Schneider, under the CC-BY-NC-SA 4.0 license.
I wonder if the ISP got charged as well lol
The charges usually end up falling onto the last one who can't stick them onto someone else.
Like, a carrier can blame the ISP, who can blame the VPN, who can check its logs and blame an address owner, who... better keep their own logs capable of identifying someone else if they're letting random people do random stuff using that address. And a good lawyer, and will and money to fight it.
It sure is weird how a political system based around who has the most money always ends up hurting the people that don't have money. Nobody could've predicted that.
From the article...
Yes, as they had to give me the minimum sentence. By law they were right as the law only protected registered companies, unlike in Germany for example. The law was changed a few weeks later to include private persons and sole traders as protected lsps, not just companies, but they had to convict me. No choice in the end.
So, ISPs in Austria actually have legal protection from liability here, rightfully so, and also rightfully so, that protection was extended to private persons as well. A rare story of a legal system apparently working well, with regard to the marriage of privacy and technology.
The law was changed a few weeks later to include private persons and sole traders as protected lsps, not just companies, but they had to convict me. No choice in the end.
I am not sure I would consider this "working well". It is the job of the court to determine if and how to apply law. Laws are never perfect and should be applied per intention, and not word-for-word. If the latter would even be possible, we wouldn't need judges in the first place, because it would be a "simple" decision tree. But it's not. And we have judges and the court processes for a reason.
If the law was amended a few weeks later, it shows, IMO, that the intention of the law was different than what was written down. Therefore the judge should have ruled that way by acknowledging that while the law does not exempt private individuals, its intention shows that it clearly should (simply because it doesn't make much sense otherwise).
In other words: if the system really worked well, the judge would have sentenced (or rather not sentenced) within the intention of the law, and not within the strict writing.
(Worst case is that something like that gets escalated to the highest court who then either also accepts or overrules it.)
Shouldn't all social media, ISPs, Apple, Google, etc also be found guilty of the same crime then? What about CDN?
you see, they are companys and they make monzees that they dont pay taxes on, so its fine. But that guy was a terroristic web activist, subverting the order of the free world by providing free tools to a community of which some used it for illegal purposes.
The article explains that this was basically a flaw in the way the law was written
The absolute balls on the man to continue after being raided. It's unfortunate that the private internet requires people like him to risk their safety so it can continue to operate.
Reading the article, it's not just distributed CP. Someone also used his Tor Exit to hack into a NATO facility in Poland that dealt in chemical/biological weapons. Like, yeeesh.
This “someone” sounds an awful lot like a nation-state actor.
Yikes 😬
I am from austria and honestly I feel ashamed. What honestly gets my blood boiling is the fact, that there is a high chance the people that connected through his exit node are probably still free.
It is like jailing the postman for delivering a letter containing CP. Anyway I hope the people actually actively distributing and using CP get what they deserve.
Here the crime is privacy, which is the same thing many countries are trying to curtail, including France, which is clamping down hard on encryption.
With time we will see services like protonmail or vpns vilified in order to make them inaccessible to the public.
You shouldn't feel too ashamed, in the end Weber got 5 years of probation on the sentence of "support of general distribution", and shortly after the law was amended to give private persons like Weber the same protection from liability that ISPs enjoy from how people use their network. At least, according to Weber.
I'm surprised this doesn't happen more often. Home routers are trivial to compromise, and compromised home routers can also be used to distribute illegal content.
I always read this is why you run a relay as an individual not an exit. Some one has to run a exit at some point though.
You don't need an exit node to browse Tor hidden sites. Acting as a relay middle node is also not a problem.
Exit nodes are kind of a "plausible deniability" thing for Tor users from places where using Tor might be frowned upon, but otherwise you can find anything you may want to use Tor for, on hidden sites themselves.
For as much as I'd like to help the Tor network and the idea of free speech, articles like this are why I'd rather let the CIA and other national sponsors take the brunt of running those exit nodes.
But someone somewhere has to be an exit node. Not you, necessarily, in order to browse, but somebody has to be running them. Right?
Tor hidden sites are hosted on Tor nodes, so you don't leave the Tor network to browse them.
Anyone with a Tor node can host a hidden site, and there are some more or less famous ones around. Some open web sites keep a hidden one as an alternative in case their domain gets taken down or blocked for whatever reason in whatever country.
Only to connect back to the normal internet. Entry nodes are different (no clue if you can do both on the same server or not.
This is equivalent to a criminal running into a crowd to get away from police, and the police just stopping, arresting, and charging the first person in the crowd that they see for not doing anything to stop them.
Btw, what’s the current judicial status of exit nodes around the world? Why was he charged, yet the isp wasn’t? Would the isp be charged if it ran a similar exit node, or is it strictly because it was a private entity?
Rule of thumb: You get the blame.
TL;DR: Ask a lawyer.
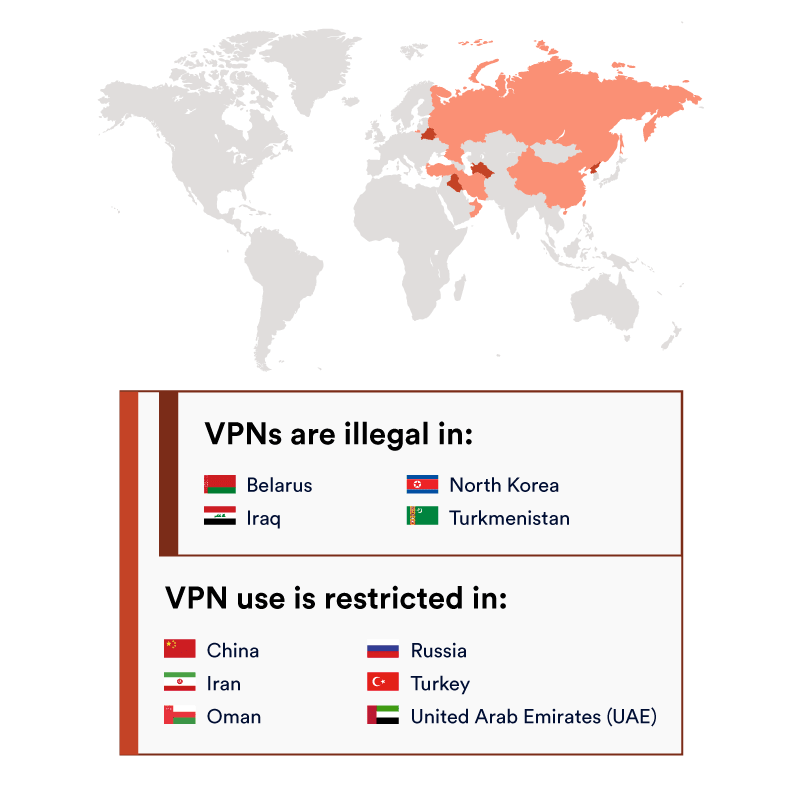
You can compare them to VPNs for the severity of restrictions (in 2020):
For some more historical info, there is this list on Wikipedia: https://en.m.wikipedia.org/wiki/Tor_(network)#Reception,_impact,_and_legislation
For a more US-centric FAQ, you can check: https://community.torproject.org/relay/community-resources/eff-tor-legal-faq/
Still, most countries don't like random people to let other unidentified random people to do random stuff, most police officers are ill equipped or educated to deal with it, legislation hasn't been tested in most places, and you're running a hard to define, changing, and sometimes random level of risk.