A hash has a fixed length, including MD5. There's no reason to cap password (input) Iength. You can hash the whole bible and still get the same length hash. So either they don't even hash it, they're idiots, or they try to be unnecessarily cautious to avoid some other limit / overflow, like POST max size (which would still be counted in at least KB, not several characters). The limit on what special characters you can use is also highly suspicious - that's not how you deal with injections / escaping your inputs.
314xel
Where is Captain Planet?
I'm rebooting my router every week via a crontab because some dynamic dns update process fails from time to time and I find it hanging. No time to debug the actual problem.
Yes I do, and a price increase of only $10 (so $30 vs $20) can make a big difference in sound quality for a pair of headphones for work (meetings and some music off Youtube). So it's not even about hifi (at that price range, of course not), it's about giving a shit and do a little research / testing before settling on a slightly better low end consumer product. Or, given a certain budget, maximise the quality for it, again, by doing some research beforehand, no matter what you plan to buy. But, most people are lazy.
When it comes to music, it also depends on a person's tastes. Ariana Grande sounds the same to me weather played on Sennheiser headphones or a microwave oven.
No, logins should be harder in order to be secure. Hence the addition of 2FA (which is also incompatible with your proposal).
As developers, we strive to make things more secure, not less, and unfortunately, good security always comes with the trade-off of less convenience for the user (larger entropy passwords, session expiration, captchas, etc).
Now, of course, it depends on how sensible the data in that account is. I wouldn't want this for my email account, for example, or online password manager, which are the entry gates to all my other accounts. The Kagi search engine offers the possibility to login on another device via a session URL which you can copy-paste. And this is fine, if the site / app clearly states the dangers, implemented it securely, tracks and lists the sessions and allows you to invalidate a session for all devices, and you are fine with potentially disclosing the data for that account (forgetting to log out, or disclose the session URL somewhere) - which is not much, as they don't log the searches, only the daily counts. And their use-case makes sense, people aren't used to authenticating in order to search something on the internet.
So, this should be an optional feature offering from the website / app, not built-in in the browser which would make it trivial to be abused by anyone.
Well, that's what you get for hosting on a Windows server. XAMPP / WAMPP should only be used for local development environments. And I'm sure they still have horrible non-production config defaults.
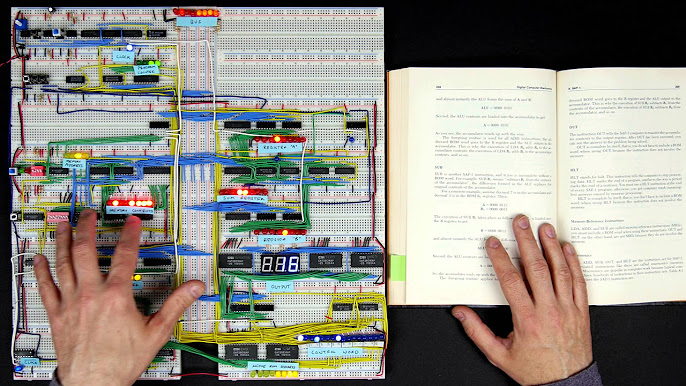
The design is so geeky that I would want one, even though I don't think I have a use for it.
Why did he throw the grenade to his rear?
A lot of people don't realize that coal, gas and oil are finite resources. Uneducated people don't accept the fact that oil comes from fossilized dinosaurs and it took millions of years to become oil. It's all a hoax to them.
Data is beautiful, the legend and title are awful.
Hairypotterism

I second the idea of a VPN instead of directly exposing devices or software to the internet. Requires more work and learning but it's more secure. I would argue that well-known VPNs are more scrutinized and pentested than any camera software ever.